displaying
Use # to search tags and @ for authors

By Multiple Authors | ArcGIS Hub |
Shawnlei Breeding shares her strategies for engaging volunteers and stakeholders to help protect eagles across The State of Florida.

By Shane Matthews | ArcGIS Online |
Esri's Basemaps continue to improve with over 300 new and updated communities, spanning 4 continents.

By Multiple Authors | ArcGIS Hub |
Hubs provide a virtual place for collaboration and engagement to happen within communities of all types and sizes.

By Owen Evans | ArcGIS StoryMaps |
Image gallery has made its way to briefings, and you can highlight a feature in a map by showing its pop-up.
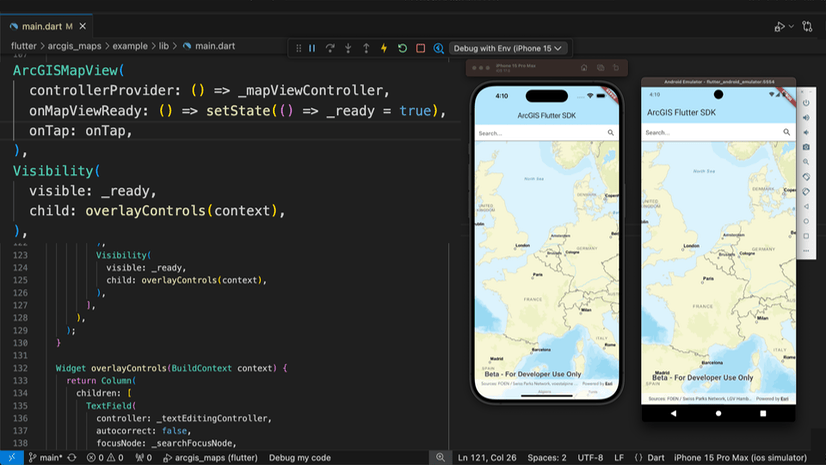
By Multiple Authors | Developers |
We are excited to announce the new ArcGIS Maps SDK for Flutter beta is now available!
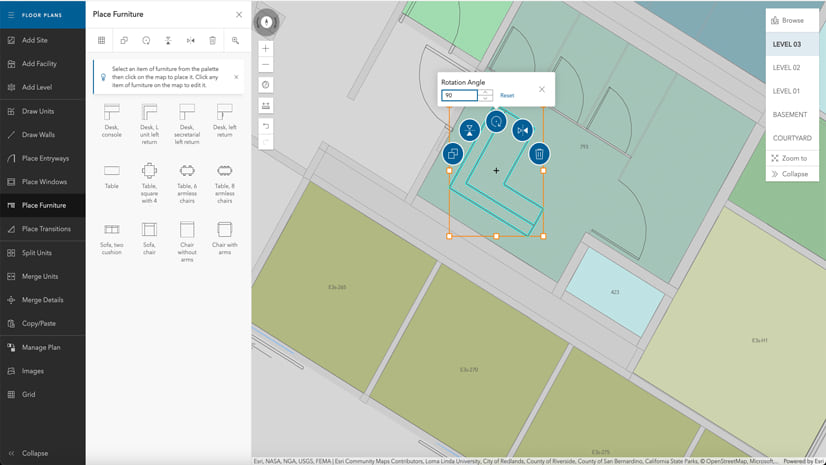
By Multiple Authors | ArcGIS Indoors |
Explore questions and answers from our webinar about Indoor GIS: Easy indoor map creation

By Field Notes Podcast |
On this season of Field Notes, we're bringing stories and tips to help you design better field workflows.

By Jeff Liedtke | ArcGIS Pro |
Format your metadata for the video multiplexer tool to geoenable video data for the Full Motion Video player.

By Multiple Authors | ArcGIS Enterprise |
From emergency management to utilities, journey with Mark Sanders of Entergy, as he shares his passion for GIS.
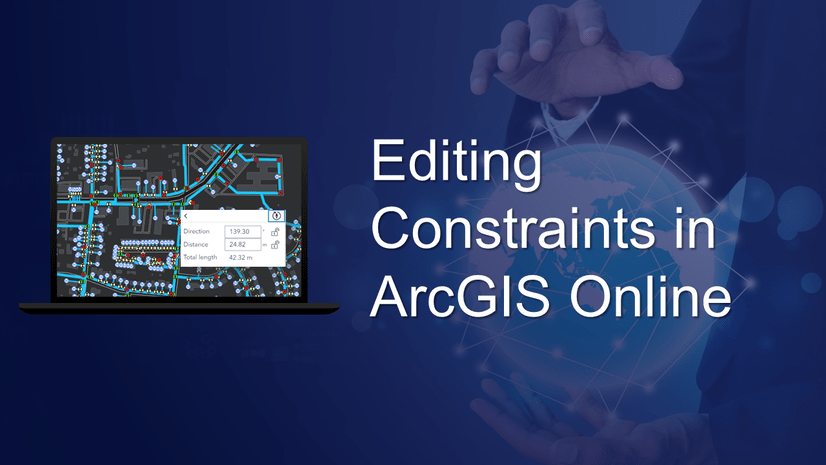
By Emily Garding | ArcGIS Online |
Get more precision while editing in ArcGIS Online using interactive tooltips to set your own editing constraints.